Generate New Ssh Pass Key
About RandomKeygen. Our free mobile-friendly tool offers a variety of randomly generated keys and passwords you can use to secure any application, service or device. Simply click to copy a password or press the 'Generate' button for an entirely new set. Password Recommendations. Jun 22, 2012 You can generate the SSH Key in a convenient location, such as the computer, and then upload the public key to the SSH key section. Then, when you create a new Droplet, you can choose to include that public key on the server. No root password will be emailed to you and you can log in to your new server from your chosen client.
- Generate Ssh Public Key From Private Key
- Generate Ssh Key
- Generate New Ssh Pass Key Lock
- Generate New Ssh Pass Key Fob
- Generate New Ssh Pass Key Replacement
You generate an SSH key through macOS by using the Terminal application. Once you upload a valid public SSH key, the Triton Compute Service uses SmartLogin to copy the public key to any new SmartMachine you provision.
Joyent recommends RSA keys because the node-manta CLI programs work with RSA keys both locally and with the ssh agent. DSA keys will work only if the private key is on the same system as the CLI, and not password-protected.
About Terminal
Terminal is the terminal emulator which provides a text-based command line interface to the Unix shell of macOS.
Generate Ssh Public Key From Private Key
To open the macOS Terminal, follow these steps:

- In Finder, choose Utilities from the Applications folder.
- Find Terminal in the Utilities listw.
- Open Terminal.
The Terminal window opens with the commandline prompt displaying the name of your machine and your username.
Generating an SSH key
An SSH key consists of a pair of files. One is the private key, which should never be shared with anyone. The other is the public key. The other file is a public key which allows you to log into the containers and VMs you provision. When you generate the keys, you will use ssh-keygen to store the keys in a safe location so you can bypass the login prompt when connecting to your instances.
To generate SSH keys in macOS, follow these steps:
Enter the following command in the Terminal window.
This starts the key generation process. When you execute this command, the
ssh-keygenutility prompts you to indicate where to store the key.Press the ENTER key to accept the default location. The
ssh-keygenutility prompts you for a passphrase.- Type in a passphrase. You can also hit the ENTER key to accept the default (no passphrase). However, this is not recommended.
You will need to enter the passphrase a second time to continue.
After you confirm the passphrase, the system generates the key pair.
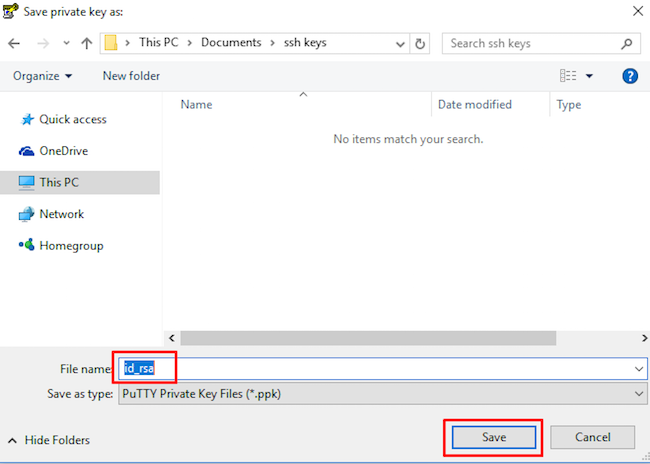
Your private key is saved to the id_rsa file in the .ssh directory and is used to verify the public key you use belongs to the same Triton Compute Service account.
| Never share your private key with anyone! |
|---|
Your public key is saved to the id_rsa.pub;file and is the key you upload to your Triton Compute Service account. You can save this key to the clipboard by running this:
Importing your SSH key
Now you must import the copied SSH key to the portal.
- After you copy the SSH key to the clipboard, return to your account page.
- Choose to Import Public Key and paste your SSH key into the Public Key field.
- In the Key Name field, provide a name for the key. Note: although providing a key name is optional, it is a best practice for ease of managing multiple SSH keys.
- Add the key. It will now appear in your table of keys under SSH.
Troubleshooting
You may see a password prompt like this:
This is because:
- You did not enter the correct passphrase.
- The private key on your Macintosh (
id_rsa) does not match the public key stored with your Triton Compute Service account. - The public key was not entered correctly in your Triton account.
What are my next steps?
Right in the portal, you can easily create Docker containers, infrastructure containers, and hardware virtual machines.
In order to use the Terminal to create instances, set up triton and CloudAPI as well as the triton-docker commandline tool.
Introduction
SSH (Secure Shell) allows secure remote connections between two systems. With this cryptographic protocol, you can manage machines, copy, or move files on a remote server via encrypted channels.
There are two ways to login onto a remote system over SSH – using password authentication or public key authentication (passwordless SSH login).
In this tutorial, you will find out how to set up and enable passwordless SSH login.
- Access to command line/terminal window
- User with sudo or root privileges
- A local server and a remote server
- SSH access to a remote server via command line/terminal window
You may already have an SSH key pair generated on your machine. To see whether you have SSH keys on the system, run the command:
If the output tells you there are no such files, move on to the next step, which shows you how to generate SSH keys.
In case you do have them, you can use the existing keys, back them up and create a new pair or overwrite it.
1. The first thing you need to do is generate an SSH key pair on the machine you are currently working on.
In this example, we generate a 4096-bit key pair. We also add an email address, however this is optional. The command is:
2. Next, type in the location where you want to store the keys or hit Enter to accept the default path.
3. It also asks you to set a passphrase. Although this makes the connection even more secure, it may interrupt when setting up automated processes. Therefore, you can type in a passphrase or just press Enter to skip this step.
4. The output then tells you where it stored the identification and public key and gives you the key fingerprint.
5. Verify you have successfully created the SSH key pair by running the command:
You should see the path of the identification key and the public key, as in the image below:
Generate Ssh Key
You can upload the public SSH key to a remote server with the ssh-copy-id command or the cat command. Below you can find both options.
Option 1: Upload Public Key Using the ssh-copy-id Command
Generate New Ssh Pass Key Lock
To enable passwordless access, you need to upload a copy of the public key to the remote server.
1. Connect to the remote server and use the ssh-copy-id command:
2. The public key is then automatically copied into the .ssh/authorized_keys file.
Another way to copy the public key to the server is by using the cat command.
1. Start by connecting to the server and creating a .ssh directory on it.
2. Then, type in the password for the remote user.
3. Now you can upload the public key from the local machine to the remote server. The command also specifies that the key will be stored under the name authorized_keys in the newly created .ssh directory: Free microsoft office key generator 2016.
With the SSH key pair generated and the public key uploaded to the remote server, you should now be able to connect to your dedicated server without providing a password.
Check whether the setup works by running the command:
The system should directly log you in to the remote server, no password required.
Note: Once you verify that you can SHH into the remote serve without a password, consider disabling SSH password authentication altogether. It will add another layer of security and secure your server from brute-force attacks.
Optional: Troubleshooting Remote Server File Permissions
File permissions on the remote server may cause issues with passwordless SSH login. This is a common issue with older versions of SSH.
If you are still prompted for a password after going through all the steps, start by editing file permissions on the remote server.
- Set permissions 700 for the .ssh directory.
- Set permissions 640 for the .ssh/authorized_keys directory.
Edit file permissions with the following command:
Enter your password when prompted. There will be no output if the action was successful. The issue should be resolved now.
If you want to automate updates and other tasks, or seamlessly SSH into a remote server, you should enable passwordless SSH login.
The instructions outlined in this article should have helped you to do so.
For more SSH commands, check out these 19 common SSH commands in Linux with examples.
And lastly our sony vegas 13 pro patch download, alsoworks with sony vegas pro 13 keygen that generates working sony vegaspro 13 authentication code. Edit SD, HD, 2K, and 4K material in 2D or stereoscopic 3D, with drag-and-drop functionality or traditional 3-point and 4-point editing modes. We allknown that everyone cannot afford to pay for sony vegas pro 13 productkey our sony vegas pro 13 patch has been designed and developed for suchusers as well as those who do not want to spend their hard earned moneyon this product. Vegas pro 11 key generator.
Next you should also read
Generate New Ssh Pass Key Fob
When establishing a remote connection between a client and a server, a primary concern is ensuring a secure…
Hackers are always on the lookout for server vulnerabilities. Minimize risks and be confident your data is…
The article covers the 5 most common and efficient ways to secure an SSH connection. The listed solutions go…
Generate New Ssh Pass Key Replacement
Rsync is a Linux tool that allows you to transfer data over SSH to a remote server securely. Use the options…